
Mastering Network Performance Optimization Techniques for IT Infrastructure
Optimize Your Network Performance Today
Reliable, high-performing networks are no longer optional — they’re essential to running a modern business. This guide lays out practical strategies for optimizing network performance so your IT infrastructure runs faster, costs less, and stays secure. You’ll get clear, actionable insights on why optimization matters, how proactive monitoring and bandwidth controls help, how security and performance work together, and why ongoing maintenance and automation keep networks healthy as you scale and meet compliance requirements.
Why Network Performance Optimization Matters for Growing and Regulated Businesses
For businesses—especially those in regulated industries—network performance affects productivity, costs, and compliance. Tuning networks to run efficiently reduces downtime, improves the user experience, and lowers the operational burden. That, in turn, supports better security and helps you meet regulatory obligations.
As organizations grow, maintaining performance while adding users and services is critical. Network optimization makes it easier to onboard new technologies and scale without surprises.
Evolution Technologies delivers managed IT services designed to implement pragmatic network optimization strategies. We help keep your infrastructure resilient and compliant so you can concentrate on running your business.
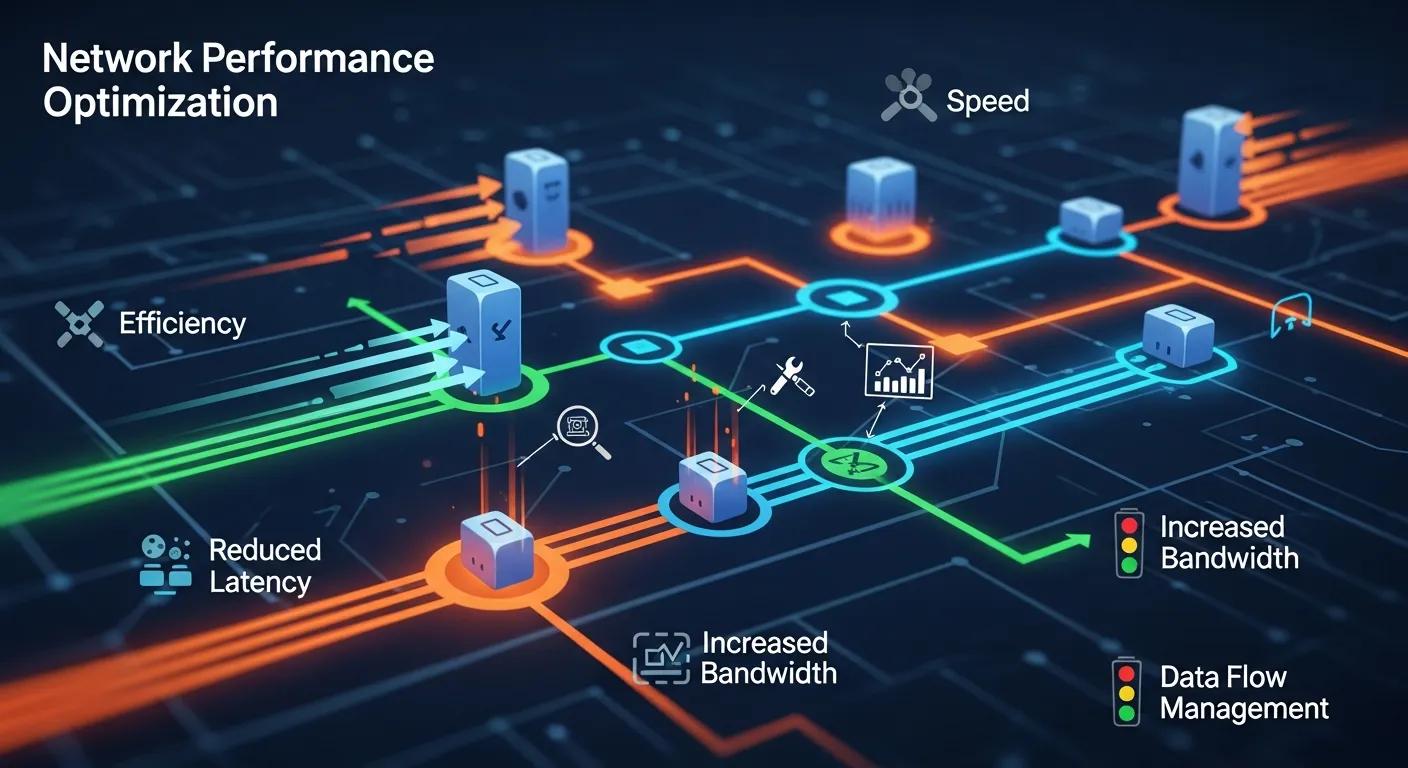
Key Benefits of Optimizing IT Infrastructure Networks
Optimizing your IT network delivers measurable benefits:
- Increased Efficiency: Faster data flows and lower latency help teams work without interruptions.
- Cost Savings: Fewer outages and better resource use reduce operational expenses.
- Enhanced Security: A tuned network is easier to secure, protecting critical and sensitive data.
How Network Optimization Supports Compliance in Regulated Organizations
Network optimization is a cornerstone of compliance. Secure, well-managed networks simplify meeting data protection and privacy requirements.
Optimized systems improve monitoring and reporting, which are vital for audits. They also make it easier to deploy and enforce security controls, lowering the chance of breaches and helping demonstrate regulatory adherence.
Taking a proactive approach to network management both preserves compliance and strengthens stakeholder trust.
How Proactive Network Performance Monitoring Improves IT Infrastructure
Continuous performance monitoring helps you spot and fix issues before they become outages. That reliability keeps services available and ensures efficient use of infrastructure.
Modern monitoring tools provide real-time analytics so IT teams can make informed, timely adjustments and tune performance on the fly.
Essential Network Performance Metrics to Track
Track these metrics to measure and improve performance:
- Latency: Time it takes data to travel—low latency equals better user experience.
- Bandwidth Utilization: How much capacity is in use, which highlights bottlenecks.
- Packet Loss: Lost packets degrade applications and indicate underlying problems.
Effective Bandwidth Management and Traffic Prioritization Techniques
Bandwidth controls and traffic prioritization ensure critical services get the resources they need while less critical traffic is deprioritized.
How Quality of Service Improves Network Traffic Flow
Quality of Service (QoS) enforces priority for latency-sensitive apps like VoIP and video, reducing congestion and ensuring predictable performance for business-critical communications.
Applied correctly, QoS minimizes delays and improves overall user experience across the network.
Common Traffic Shaping and Compression Solutions
Typical techniques to manage bandwidth include:
- Traffic Shaping: Governs how traffic is queued and transmitted to prevent congestion and ensure policy-based distribution.
- Data Compression: Shrinks payloads so more data moves across the same link, improving throughput.
How Network Security Optimization Integrates with Performance
Security and performance are complementary: integrating security into network design protects data without creating unnecessary bottlenecks.
What Role Do Firewalls and Intrusion Detection Systems Play?
Firewalls enforce access boundaries and policy-based filtering, while Intrusion Detection Systems (IDS) spot suspicious activity. Tuning these tools reduces false positives and ensures security checks don’t block legitimate traffic.
Well-configured security layers help maintain performance while protecting sensitive assets.
How Network Segmentation Improves Security and Compliance
Segmentation breaks networks into isolated zones with tailored security controls. That limits exposure if a breach occurs and makes it easier to apply compliance rules to specific areas.
This targeted approach strengthens protection while preserving performance for permitted traffic flows.
Modern IT Infrastructure Strategies Using Cloud and SD-WAN
Cloud services and SD-WAN are central to modern network strategies, offering flexibility, redundancy, and cost-effective performance at scale.
How SD-WAN Optimizes Distributed Network Performance
SD-WAN dynamically steers traffic across multiple links to prioritize critical applications, improve resiliency, and lower costs compared with traditional MPLS-only designs.
When implemented correctly, SD-WAN boosts reliability for distributed teams and branch locations.
Best Practices for Hybrid Cloud Network Architecture
Designing a hybrid cloud network typically follows these best practices:
- Ensure Seamless Integration: Standard protocols and consistent networking stacks simplify cross-environment communication.
- Implement Robust Security Measures: Use encryption and strict access controls for data in transit and at rest.
- Monitor Performance Continuously: Keep visibility across on-prem and cloud resources to optimize allocations and respond to issues.
How Continuous Maintenance and Automation Sustain Peak Network Performance
Ongoing maintenance and automation keep networks reliable and reduce manual toil. Regular updates and proactive management prevent many common failures.
Why Regular Network Audits and Firmware Updates Matter
Audits reveal configuration drift, capacity constraints, and vulnerabilities. Firmware and software updates patch known issues and enable performance improvements.
Prioritizing these tasks lowers risk and helps maintain consistent performance over time.
How Automation Streamlines Network Management Tasks
Automation handles repetitive work—monitoring, alerting, patching, and configuration tasks—so IT teams can focus on architecture and strategy instead of firefighting.
Automated workflows reduce human error and accelerate response times, improving both uptime and team productivity.
| Strategy | Mechanism | Benefit |
|---|---|---|
| Proactive Monitoring | Continuous performance tracking | Early issue detection |
| Bandwidth Management | Traffic prioritization | Enhanced application performance |
| Security Optimization | Integrated security measures | Improved data protection |
Mastering network performance optimization helps organizations keep systems reliable, secure, and cost-effective. By combining proactive monitoring, targeted bandwidth controls, and security-focused design—backed by automation and regular maintenance—you can improve both performance and compliance. For tailored guidance and implementation support, speak with Evolution Technologies about optimizing your network for the demands of today and tomorrow.
Frequently Asked Questions
What are the signs that my network needs optimization?
Common indicators include frequent outages, slow application responses, high latency, or noticeable packet loss. If users report delays, or the network struggles to accommodate new devices or services, those are clear signs to investigate. Regular monitoring helps catch trends before they cause major disruptions.
How can I measure the success of my network optimization efforts?
Compare baseline metrics (latency, bandwidth utilization, packet loss) to results after changes. Look for faster response times, fewer incidents, and improved uptime. Combine quantitative monitoring data with user feedback to get a full picture of impact.
What role does employee training play in network performance optimization?
Training helps staff use network resources responsibly and recognize issues early. Educated users follow security practices and reduce avoidable problems, while trained IT staff can better operate monitoring tools and respond to incidents—both of which support long-term performance.
Can network optimization improve remote work capabilities?
Yes. Prioritizing critical remote applications, optimizing bandwidth, and using solutions like SD-WAN can significantly improve remote user experience, ensuring reliable access to apps and data even under variable network conditions.
What are the potential risks of neglecting network performance optimization?
Ignoring optimization can cause more downtime, slower services, higher operational costs, and increased security risk. Over time, poor performance erodes user productivity and can expose the organization to compliance and reputational harm.
How often should I conduct network performance assessments?
Conduct assessments at least quarterly, and more often if your environment changes rapidly or you have strict compliance demands. Also run assessments after major updates or architecture changes to validate performance and security.
Conclusion
Effective network performance optimization is a strategic investment: it increases efficiency, lowers risk, and supports compliance while enabling growth. Combining continuous monitoring, smart bandwidth controls, security-by-design, and automation ensures a resilient, scalable infrastructure. If you’d like a tailored plan for your environment, Evolution Technologies can help you prioritize and implement the right improvements. Start optimizing your network today.




